SHARE THIS ARTICLE
Best Security Protocols in Modern Cryptocurrency Exchange Development

Cryptocurrency exchanges play a central role in the digital asset ecosystem, allowing traders, investors, and institutions to buy, sell, and manage cryptocurrencies on a large scale. Over the last decade and a half, the crypto market has expanded from a niche experiment to a multi-trillion-dollar money market in the world.
Yet this growth also has increased threats against these platforms. Between 2009 and 2024, accumulated losses with security breaches at crypto exchanges amounted to over $8.494 billion, thus emphasizing the critical importance of efficient security protocols in the development of exchanges.
As centralized exchanges (CEX) and decentralized exchanges (DEX) evolve and grow, the face of security has transformed from a series of basic defenses into a complex and real-time protection mechanism. Modern users are not just expecting decent trading and high liquidity but also assurances that their assets and their personal data are not accessed by increasingly sophisticated adversaries.
For businesses looking to invest in professional cryptocurrency exchange development services, cryptocurrency security protocols are at the forefront of the components needed to ensure user trust, regulatory compliance, and long-term success.
This blog explores the optimal security protocols used in the contemporary development of a cryptocurrency exchange, their operations and importance to create prevalent secure, scalable and compliant trading platforms.
Core Security Protocols in Modern Crypto Exchanges
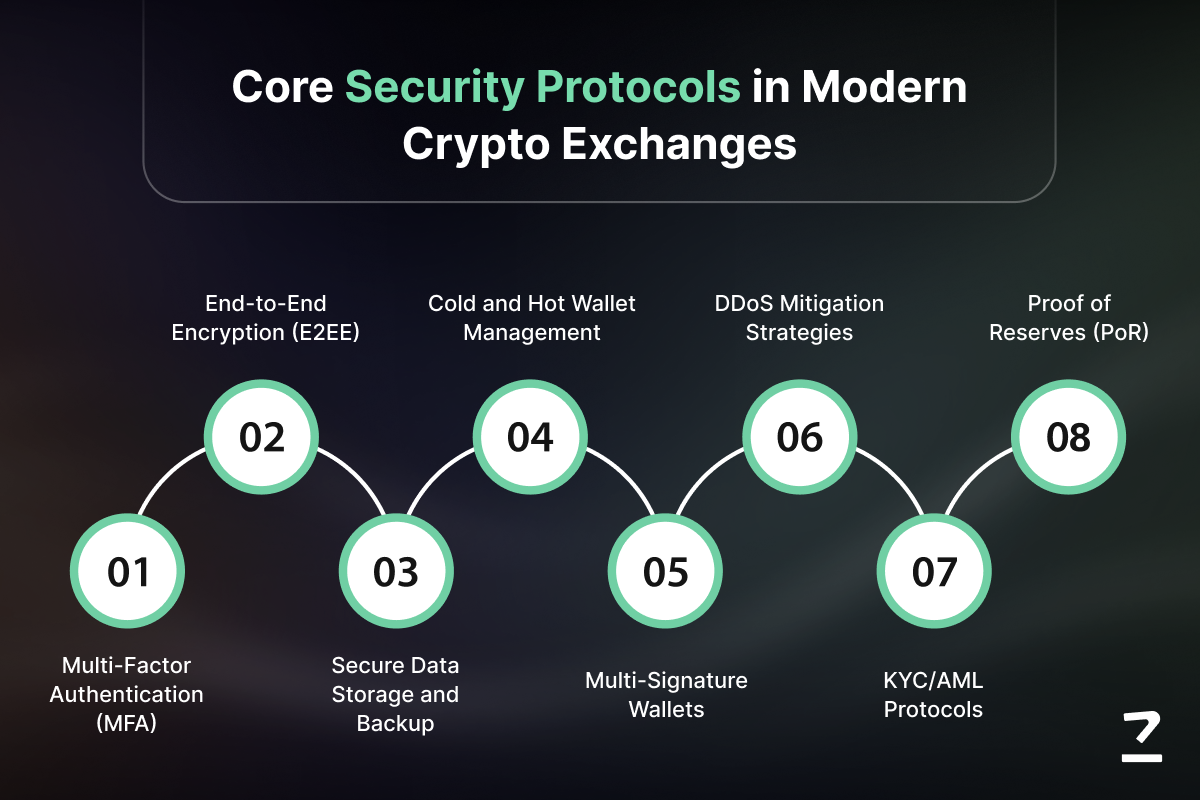
Security in a cryptocurrency exchange needs to deal with several levels of security such as security of access, data, transaction and infrastructure hardness and regulatory requirements. Combining these layers forms a defense-in-depth architecture, which addresses various attack vectors.
User Authentication and Access Control
A secure exchange starts with the question of who gets access to what and how they establish their identity.
-
Multi-Factor Authentication (MFA)
Passwords alone are weak. MFA requires all users to authenticate with more than one factor, but the common combination is something the user knows (password), something the user has (authenticator app or hardware key), and something the user has (biometrics). This does raise the bar for attackers trying to compromise accounts. -
Role Based Access Control (RBAC)
Not all users or staff should be given the same privileges. Implementing RBAC ensures that sensitive operations such as those related to managing wallet keys, or those pertaining to administrative controls, are limited to authorized personnel, reducing the risk within your system. -
Biometric Verification
For high-value transactions or important workflow approvals, biometric verification (such as fingerprint or facial) provide an additional and non-replicable security factor to supplement traditional MFA.
Data Protection Protocols
Protecting sensitive data and credentials in storage or transmission by the exchange is paramount. Encryption and secure storage practices are such that even if data is intercepted, it will be unintelligible to unauthorized parties.
-
End‑to‑End Encryption (E2EE)
All data, when at rest or in transit, should be protected behind encryption standards such as SSL/TLS for communication channels and AES-256 for data stored. This helps to prevent data breaches through interception of the network. -
Secure Data Storage and Backup
User records, transaction information, and private keys must be kept securely and backed-up in encrypted forms. Redundant backups across environments that are isolated from each other help in preventing the loss of data in case of infrastructure failures or malicious attacks. -
Data Masking and Tokenization
Sensitive fields like personal identifiers or wallet keys should be replaced with obfuscated values for regular processing or analysis. Tokenization ensures that actual sensitive data is never exposed in the process of intermediate operations.
Transaction Security Measures
Protecting the value transfers that actually occur in the exchange requires special controls in addition to basic authentication.
-
Cold and Hot Wallet Management
In order to allow trading and withdrawals, exchanges usually keep a portion of their total assets in online 'hot wallets'. The bulk (often 90-95 %) is held in offline "cold wallets" which are not accessible via internet-connected systems. This significantly reduces the attack surface on thirteen asset holdings. -
Multi‑Signature Wallets
Multi-Sig wallets need more than one independent signature to approve a transaction, removing the threat of using a single hacked key to empty funds. Many modern exchanges also use Multi-Party Computation (MPC), which spreads private keys around multiple nodes even further minimising central points of failure. -
Transaction Monitoring and Alerts
Real-time transaction monitoring is the use of pattern recognition and automated alerting to detect suspicious activity such as large withdrawals from new IP addresses or rapid series of trades. This allows immediate intervention to avert unauthorized transactions.
Network and Infrastructure Security
The infrastructure that provides the underlying exchange must be available and secure from disruption from outside entities and vulnerabilities from within.
-
Firewalls and Intrusion Detection Systems (IDS)
Web Application Firewalls (WAF) help to protect against common web exploits, while IDS tools help to monitor traffic patterns for indications of intrusion and can help to block malicious activities early on. -
DDoS Mitigation Strategies
Distributed Denial of Service (DDoS) attacks target the server of the platform to overwhelm it into downtimes or abnormal services. DDoS protection service and traffic filtering make the platform available despite the high loads of attack traffic. -
Secure API Integration
APIs have made it possible for critical functionality such as order placement, market data feeds, and third-party integrations. Secured APIs involve the use of token-based authentication (e.g., OAuth 2.0), rate limiting (to block brute force attacks), and stringent input validation (to prevent exploitation).
Compliance and Regulatory Standards
Security is not just about systems and code; it should be in line with legal systems and industry expectations.
-
KYC/AML Protocols
Know Your Customer (KYC) and Anti-Money Laundering (AML) checks help to confirm the identity of users and prevent bad actors from exploiting the exchange. Tools such as live selfie and geo tagged verification have been recently enforced by regulators in jurisdictions such as India to strengthen the enforcement of AML. -
Proof of Reserves (PoR)
Proof of Reserves enables exchanges to cryptographically demonstrate to the users that their assets are completely backed. This transparency is needed to build trust, especially after high-profile collapses in the industry, and is increasingly demanded by sophisticated users. -
Security Certificates and Audits
Certifications such as the ISO 27001 or the SOC 2 offer some independent assurance that security controls comply with recognized standards. Regular penetration testing and third-party audits can further ensure that vulnerabilities are identified and proactively remediated.
Emerging Security Trends in Crypto Exchange Development Beyond 2026
While basic protocols help secure today's exchanges, forward-thinking platforms must leverage future security technologies if they are to stay ahead of the threat curve when it comes to using cryptocurrency exchange development services.
Passwordless and Biometric Authentication
Moving beyond passwords to biometric and token-based authentication is good for reducing attack surfaces and enhancing usability. Biometric verification makes sure the user proves his or her identity using physical features that are more difficult to compromise than passwords alone.
Adaptive Multi‑Factor Authentication
Adaptive MFA adjusts the authentication requirements dynamically based on contextual signals like device, location and transaction size. This provides balance between security and user convenience without sacrificing security.
AI‑Powered Fraud Detection
AI and machine learning is used to analyze huge amounts of trading and account activity to spot patterns that signify fraud (e.g., exploits of flash loans or layered withdrawals). These systems mark the anomalies for automated, or analyst review for faster threat response.
Predictive Threat Modeling
Predictive threat modeling gives you a way to simulate attack vectors on system elements (wallets, APIs, smart contracts) to identify weaknesses before they are exploited. This is a proactive approach to reduce reactionary security costs and avoid breaches.
Post‑Quantum Cryptography (PQC)
Quantum computing is a long-term threat to classical cryptographies. PQC algorithms such as lattice based cryptography are designed to make digital signatures and key exchanges safe from quantum-enabled attacks, future-proofing platforms as computing power develops.
Decentralized Identity (DID) Systems
DID frameworks offer their users control over their identity information, which allows for privacy-preserving know your customer (KYC) while ensuring compliance. Blockchain-based identity can minimize the centralized data repositories that are targets for breach.
Common Threats and Attack Vectors
Despite the advanced protection, exchanges are still targeted for different types of attacks. Understand attack vector threats for designing resilient platforms below.
-
Hot Wallet Vulnerabilities: Hot wallets are online and, as such, are inherently more dangerous. Historical incidents such as the WazirX hack in 2024, which ended in a loss of around $234.9 million in capital, are important examples of how hacked wallets could annihilate platforms and users.
-
Smart Contract Exploits: DEX platforms use smart contracts, which may have subtle logic flaws. Without serious auditing and formal verification, attackers can take control of contracts to drain money out of them or derail markets.
-
Phishing, Malware, and DDoS Attacks: Phishing attacks, attacks on authentication devices with malicious software, and DDoS attacks are very common. Educating users and strengthening infrastructure against those threats is essential.
-
Insider and API Vulnerabilities: Internal threats and insecure APIs can open up sensitive functionality. Strict access controls, audit trail, and API hardening (rate limiting, token systems) help mitigate these vectors.
Best Practices for Secure Crypto Exchange Development

Executing secure development demands for disciplined practices right from initial design to deployment and continued maintenance while availing the best cryptocurrency exchange development services.
-
Input Validation and Secure Coding: Input validation, whitelisting of accepted formats, and characters escaping are used to prevent injection attacks and unauthorized code execution. Secure coding standards and code reviews minimize logic vulnerabilities before the code is released.
-
Secure Authentication and Session Management: A combination of robust MFA, session expirations, and least-privilege access ensures that attackers cannot take advantage of stale sessions or overprivileged accounts.
-
Data Encryption and Error Handling: Encrypting all sensitive data and making sure that error messages do not reveal any internal data is a way of ensuring data integrity and user privacy.
-
Continuous Testing and Vulnerability Management: Regular penetration testing, automated code scanning and bug bounty programs help to keep security defenses on their toes and ready to adapt to new challenges.
Choosing the Right Cryptocurrency Exchange Development Partner
Selecting the right cryptocurrency exchange development company is an important step in creating a secure, scalable, and compliant cryptocurrency exchange. The perfect partner is more than just a coder, and a combination of profound knowledge in blockchain technology, security protocols and a thorough knowledge of regulatory obligations to make sure your platform is running safe and efficiently.
A strong partner ensures security is embedded at every layer from cold storage, to multi-signature wallets, to using multi-factor authentication and DDoS protection. Regulatory compliance such as KYC, AML, Proof of Reserves is embedded in the platform, which minimizes legal risks and builds trust from the users.
Important Factors to Consider When Choosing A Cryptocurrency Exchange Development Services Partner:
-
Security-First Approach: Ensure the security-first approach in partner is in place such as separation of hot and cold wallet, real-time monitoring, regular penetration testing, vulnerability auditing, etc. Security should be proactive not reactive.
-
Proven Expertise & Portfolio: Review their experience in the development, launch, and maintenance of centralized (CEX) and decentralized (DEX) exchanges. Case studies, client testimonials, and security certifications are great signs of reliability.
-
Regulatory Compliance & Legal Knowledge: The partner has to be knowledgeable of AML, KYC and other global financial regulations. Knowledge on different jurisdictions ensures that your exchange is compliant as it scales internationally.
-
Scalability & Performance: Look for partners who can design high-performance architectures with the ability to scale with high transaction volumes and user growth without compromising stability and security of the platform.
-
Customization & Technology Stack: The team should provide customized solutions that have a flexible architecture, support for the latest blockchain technologies, APIs and integration capabilities. Customization secures your exchange with certain business requirements.
-
Post-Deployment Support: A reputable exchange development services provider provides post-deployment support, such as maintenance, updates, performance monitoring, and security audits. This will ensure that your exchange is resilient, adaptive, and secure as threats and technologies change.
Future‑Proofing Crypto Exchanges for Long-Term Growth

In the rapidly evolving crypto ecosystem, exchange building is not a matter of launching success, it's a matter of longevity. Modern exchanges need to be built to scale, adapt, and survive - from technological and market perspectives.
Key strategies for future proofing include:
-
Microservices-Based Architecture: By breaking the exchange up into independent parts, updates, security patches, and feature expansion can be implemented without any disruption to the whole platform. This provides ongoing availability and flexibility when the number of users increases.
-
Cloud Scalability and Redundancy: By using the cloud infrastructure, exchanges can manage spikes in trading volume, particularly during periods of market volatility, without incurring downtime and poor performance. Redundant systems guarantee that operations continue even in the event of an outage or failure.
-
AI-Driven Threat Detection: Advanced analytics and machine learning systems are capable of anticipating and neutralising new attack vectors in real-time with the ability to identify sophisticated fraud, flash loan exploits and anomalous transaction patterns.
-
Smart Contract Auditing and Verification: In the case of DEXs and hybrid platforms, smart contract auditing is essential to help prevent the existence of smart contract vulnerabilities and exploits before they can affect the assets of users.
-
Disaster Recovery and Business Continuity Planning: Comprehensive strategies to assure that critical services, wallets, and user data are secure and recoverable in the event of catastrophic incidents, such as cyberattacks or infrastructure failures.
Building a Secure and Trustworthy Crypto Platform with Codezeros
Modern exchanges need to move beyond the most basic of defenses; they need to add multi-signature wallets, cold storage, advanced encryption, and ongoing monitoring to ensure that user assets remain safe at all times. By implementing robust operational, infrastructure and compliance protocols, platforms can secure themselves from the common vectors of attack, from hot wallet breaches to phishing attacks and smart contract exploits.
Future-proofing and resilience play a similarly important role. Scalable architectures, AI-based threat detection, smart contract auditing and disaster recovery strategies help exchanges adapt to changing market conditions and new cyber threats. This way, not only does it minimize risk, but it also boosts user confidence, regulatory credibility, and overall longevity of the platform, paving the way for sustainable growth in a highly competitive landscape.
Businesses can leverage a reliable Cryptocurrency Exchange Development Company such as Codezeros to create a secure, compliant, and scalable platform that suits their goals. If you are seeking security-first design, built-in regulatory compliance, and continuing monitoring, then connect us to deliver exchanges that inspire trust, safeguard assets, and keep going in the face of evolving threats, providing businesses a competitive edge and a peace of mind together into the future.
FAQs:
1. What are the top security features every modern crypto exchange should have?
Look for Multi-Sig/MPC wallets, Cold storage for most funds, Advanced Encryption (AES-256/SSL-TLS), MFA/2FA, real-time monitoring and DDoS protection. Strong API security and withdrawal whitelisting are also a necessity.
2. Why do crypto exchanges store most assets in cold wallets?
Cold wallets are offline inherently and therefore are not vulnerable to hacking on the internet. Best practice is to place around 95-98 % of funds in cold storage for the protection of large asset pools.
3. How does Proof of Reserves (PoR) improve trust in a crypto exchange?
PoR enables users to cryptographically confirm that the exchange contains assets worth the same as user balances. Regular third-party audited PoR draws in transparency and credibility.
4. What common attack vectors target exchanges today?
Attackers use hot wallets, poor access controls, smart contract bugs, phishing/social engineering, API bugs and lack of monitoring.
5. How do exchanges detect suspicious activity in real time?
AI and machine learning systems analyze transaction patterns, sounding the alarm at phenomena like exploits of flash loans or clusters of rapid withdrawals.
6. What should users look for when choosing a secure crypto exchange?
Choose exchanges: Extensive use of cold storage, MPC key management, regular PoR auditing, robust use of MFA/ Biometric logins, transparent security policies, and robust KYC/AML Compliance.
Post Author

As a distinguished blockchain expert at Codezeros, Paritosh contributes to the company's growth by leveraging his expertise in the field. His forward-thinking mindset and deep industry knowledge position Codezeros at the forefront of blockchain advancements.
Build a Secure and Scalable Crypto Exchange with Codezeros
Partner with Codezeros, a leading Cryptocurrency Exchange Development Company, to create secure, compliant, and scalable trading platforms. From multi-signature wallets and cold storage to AI-driven threat detection and regulatory compliance, we integrate advanced security protocols at every layer. Ensure your exchange protects user assets, mitigates risks, and gains trust while staying future-ready. Connect with us to develop an exchange that combines performance, safety, and long-term resilience.
Blogs
Our Latest Blogs
Discover valuable industry insights and stay up-to-date with the latest updates by exploring our curated collection of recent blog posts.
Let us know your requirement
We know ideas matter, we are the product of one. We Provide Full Assistance In Your Business



